What is it?
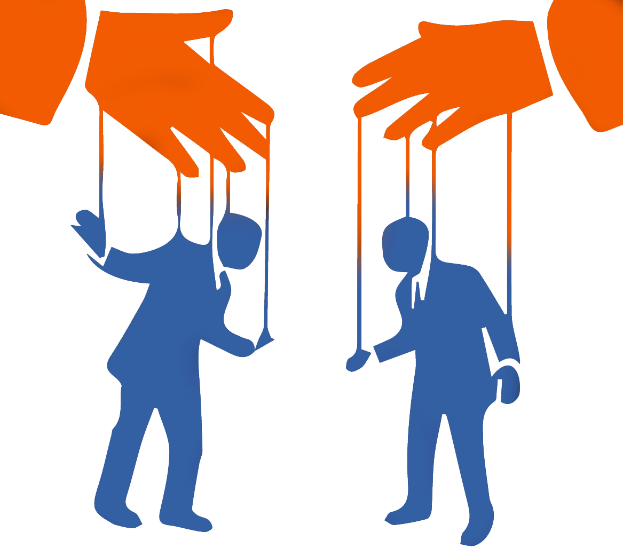
Social engineering is the process by which sociological principles are applied to specific social problems. In simpler terms, it is the exploitation of social relationships or behaviours to achieve a desired result. You could also call this manipulation. For our purposes, however, we will define social engineering as the manipulation of people for the purpose of gaining something from them.
How does it work?
Social engineers use a number of psychological tricks to make you feel like you should do what they ask. I’m sure that we all know someone who has received an email from the prince of some obscure African country who needs a few thousand dollars to ease the suffering of his people. The humble prince goes on to describe the terrible conditions his people must endure in gruesome detail. He then adds that they have a clinic full of starving children who will die unless they receive aid immediately. Hopefully, that person who you know didn’t fall for it, but there are elements of this attack which are commonly used in social engineering.

Although it may seem silly, these types of attacks work on real people all the time. There are several tricks used in this particular example that we can analyse in order to better understand why attacks like these occasionally work.
First trick, the sender of the email claimed to be in a position of authority. Most people subconsciously ascribe respect to important sounding titles. If we believe that the sender is important then we are more likely to listen to what they have to say. As a more realistic example, you are more likely to send your login credentials to someone claiming to be your boss than you are to someone claiming to be a co-worker.
Second trick, the sender tried to trigger an emotional response. By describing the suffering of his people, the sender inspired sympathy. In general, humans are emotional creatures. If an attacker can shift your decision making process to be more emotional than logical, you are less likely to recognize the incongruences of their request.
Third trick, the sender inspired a sense of urgency. Social engineers often use a tone of urgency in their wording to get people to act before they have had time to think.
Attacks like the one we just analysed are easy to spot, but a targeted attack from a more sophisticated hacker can be very difficult to identify. Unlike the sender posing as an African prince, a skilled social engineer will research their intended victim. They will look for personal information such as:
- Names of family or friends
- The establishments you frequent
- Birthdates
- Names of services you use
- Standard practices within your organization
Although this information may be considered safe for public ears, it is commonly used by hackers to get past their victims’ defences and establish a sense of trust.
Once trust has been established, the attacker then exploits that trust to gain access to sensitive information about you or your organization.
How to avoid it?
It’s estimated that less than 5% of phishing attacks target software vulnerabilities on your workstation, whereas more than 95% target the actual user in an attempt to get them to divulge sensitive data or download a malicious document. Here are some tips on how to avoid falling victim to most phishing attacks:
- Don’t open emails in the spam folder or emails whose recipients you don’t know.
- Don’t open attachments in emails from senders whom you do not know.
- Use a reputable antivirus software and perform regular scans.
- Most important of all: participate in training on how to avoid social engineering attacks.
In the last year there’s been a meteoric rise in phishing attacks, resulting in US$3.1 billion in losses in 2016 alone.
Hackers are now getting the sort of results marketing professionals could only dream of, with people six times more likely to click on a phishing email than a genuine one.
Can you spot a phish? Test your skills with the Sophos Spot the Phish game. Will you avoid the phishing net, or take the bait? Play and find out at https://www.sophos.com/spotthephish
Sophos Spot the Phish
Please read the Don’t Take the Bait whitepaper to learn more about phishing and, crucially, how to ensure your organization doesn’t get hooked.
Read Don’t Take the Bait
At Macnair we are always happy to assist you with any questions you have about Phishing Threat. Simply call me on 02 8814 5011 or shoot through an email to info@macnair.com.au and I’d be more than happy to answer your questions or ease your mind.
Brad Lynch | Macnair | blynch@macnair.com.au
- Five Eyes Nations Warn MSPs of Stepped-up Cybersecurity Threats - 13 July 2022
- Device as a Service (DaaS): Your Next Business model? - 14 May 2022
- 4 Ways to Strengthen Your Firm’s Cybersecurity Infrastructure to Prevent an Attack - 15 February 2022